Trusted Access Is Best Positioned for Which Three Use Cases
May 28 2021 CCNA Security v20 Answers 2 Comments. It is a standard-based model for developing firewall technologies to fight against cybercriminals.

15 Mobile App Design Best Practices
Qn1Our trusted multitenant cloud means you get.
. Refer to the exhibit. Changes the data in its datasource. One down the left side of the datasheet and the other across the top.
What are the terms for. Is a SQL command that instructs the Microsoft Access database engine to return info from the database as a set of records. To provide a channel for users to request and receive standard services B.
Develop the buffer memory. ACLs provide individual access control to resources. Which of the following BEST describes the purpose of access management.
Access control and the CISSP certification. Qn2The Salesforce API is. Although commonly used in Denial of Service attacks a buffer overflow attack can exploit vulnerabilities or flaws in certain applications and protocols that will allow unauthorized access.
CUnderstand the Salesforce Architecture. How Trusted Access Improves Functionality. Access is limited to the time of day a person is expected to work.
Secure the intranet communications between office A and Office B and the extranet communications with networks of partner A and partner B as. Access control has a set of associated terminology used to DESCRIBE ITS ACTIONS. If the question is not here find it in Questions Bank.
Provides the rights for users to be able to use a service or group of services C. Enable Trusted Access on an SSID. Controlling access to.
Please note that these examples are for illustrative purposes. They neither reflect all instantiations of each use case nor are they comprehensive of all code signing use cases. Enter the username and password for a user you provisioned Trusted Access for in Step 3.
Guidelines for security policy development can be found in Chapter 3. The device will be added and you will be forwarded. A circular linked list is a linked list in which the link field of the tail node link to the head node.
An organization that wanted to secure access and communications within its intranet and extranet parts hires you to provide security solutions according the following requirements. Aug 21 2017 Last Updated. Meraki Trusted Access is the easiest way to securely connect devices without an MDM.
Users are subsequently limited to access to those files that they absolutely need to meet their job requirements and no. Enter a device name select a device type Mac or iPhoneiPad and click Add Device. If you wish you can click on Print and print the test page 3.
Privileges are granted to persons based on membership in one or more functional groups. It is an ongoing effort to protect Internet. Use only extended access lists.
Youre trying to explain the basics of security to her in as short a period of time as possible. You can configure Meraki Trusted Access in 4 simple steps. This policy setting determines which users can set the Trusted for Delegation setting on a user or computer object.
The purpose of an attack against access controls is to gain access to a system. User access security demands that all persons or systems who engage network resources be required to identify themselves and prove that they are in fact who they claim to be. Calculates a sum average count or other type of total on records and then groups the results by two types of info.
Qn1When identifying processes to bring into Salesforce look for. BDiscover Use Cases for the Platform. Upon logging in since this user does not yet have any Trusted Access devices you will see the Add a device page.
An acceptable use policy defines the acceptable level of access to information assets for different users. It is a standard-based model for developing firewall technologies to fight against cybercriminals. Firmware signing driver signing trusted application stores and application software signing.
Access control is a core concept in cybersecurity so naturally its covered on the CISSP certification examCISSP domain 5 covers identity and access management and objective 54 within that domain is Implement and manage authorization mechanismsThere are six main types of access control models all CISSP. Press Ctrl F in the browser and fill in whatever wording is in the question to find that questionanswer. To detect security events.
Security account delegation. By keeping watch over network devices IT teams are able to respond rapidly to any intrusion or suspicious activity. Most directories follow a hierarchical database format based on the X500 standard and a type of protocol as in Lightweight Directory Access Protocol LDAP that allows subjects and applications to interact with the directory.
Role-based access control is BEST defined as an authorization system by which. Do not access random elements from the linked list. The developer can use a circular linked list in the following use cases.
You can take all the tests as many times as you choose until you get an A 6. CCNA Security v20 Practice Final Exam Answers 100. This section describes four example use cases.
An administrator first configured an extended ACL. A newly hired junior administrator will assume your position temporarily while you attend a conference. Describes the best practices location values policy management and security considerations for the Enable computer and user accounts to be trusted for delegation security policy setting.
Which of the following best describes an ACL. ACLs arent used in modern systems. Apply the ip access-group command inbound.
A separate user account is created for each functional role a person has. Brute-force and dictionary attacks are both password-cracking methods. An organization is trying to decide which type of access control is most appropriate for the network.
Qn2Three use cases for Finance on the platform are. Fault - tolerant computers contain redundant hardware software and power supply components. Remove the vty password since the ACL restricts access to trusted users.
The current access control approach is too complex and requires significant overhead. Enabling Meraki Trusted Access is simple. To prevent problems and resulting Incidents from happening D.
Meraki Trusted Access is enabled when you have both Meraki MR access points and Meraki Systems Manager in your network. Most enterprises have some type of directory that contains information pertaining to the companys network resources and users. When you want to take a testclick on anyone of the tests for that Study Set 4.
ITC Final Exam Answers Which statement describes cybersecurity. Click on Check Answers and it will score your test and correct your answers 5. This endpoint monitoring combined with methods that prevent access to sensitive data and applications like Trusted Access MDM features serves as another layer of protection.
A limiting access b limiting technology c and the three roles given to individuals in relationship to Access Control. Management would like to simplify the access control and provide user with the ability to determine what permissions should be applied to files document and directories. It is a framework for security policy development.
Insert the element in any position of the list.
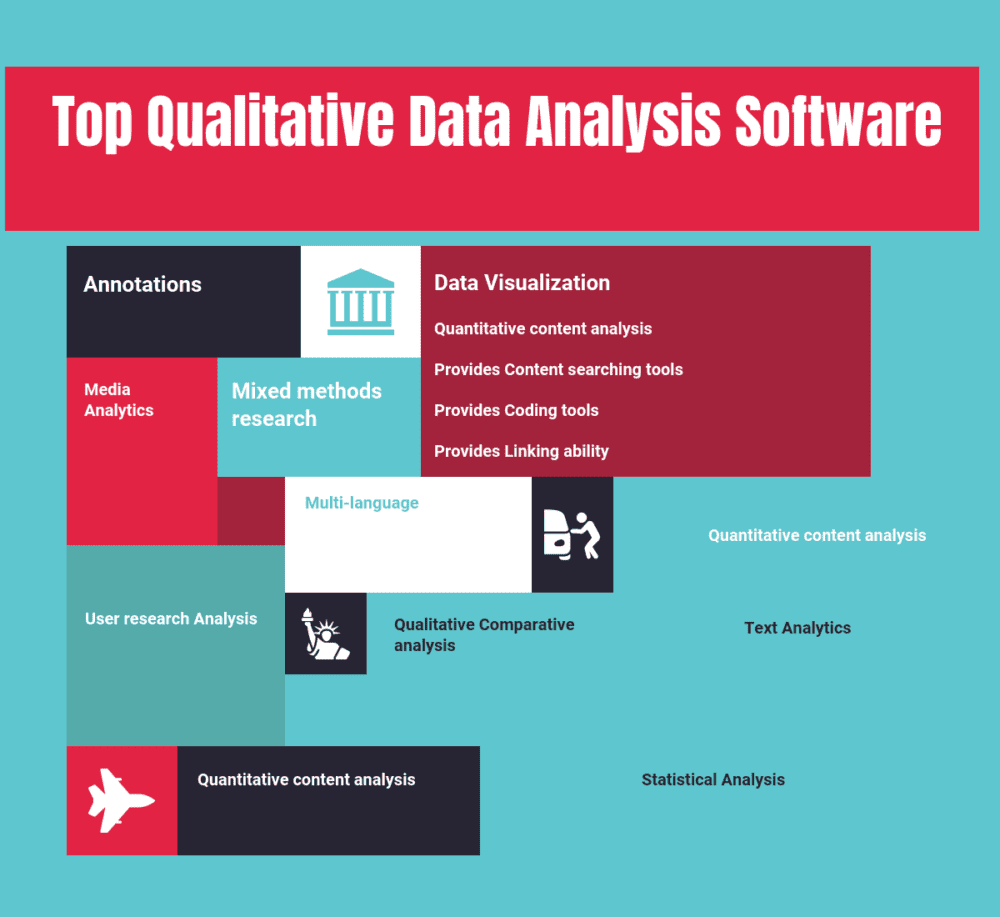
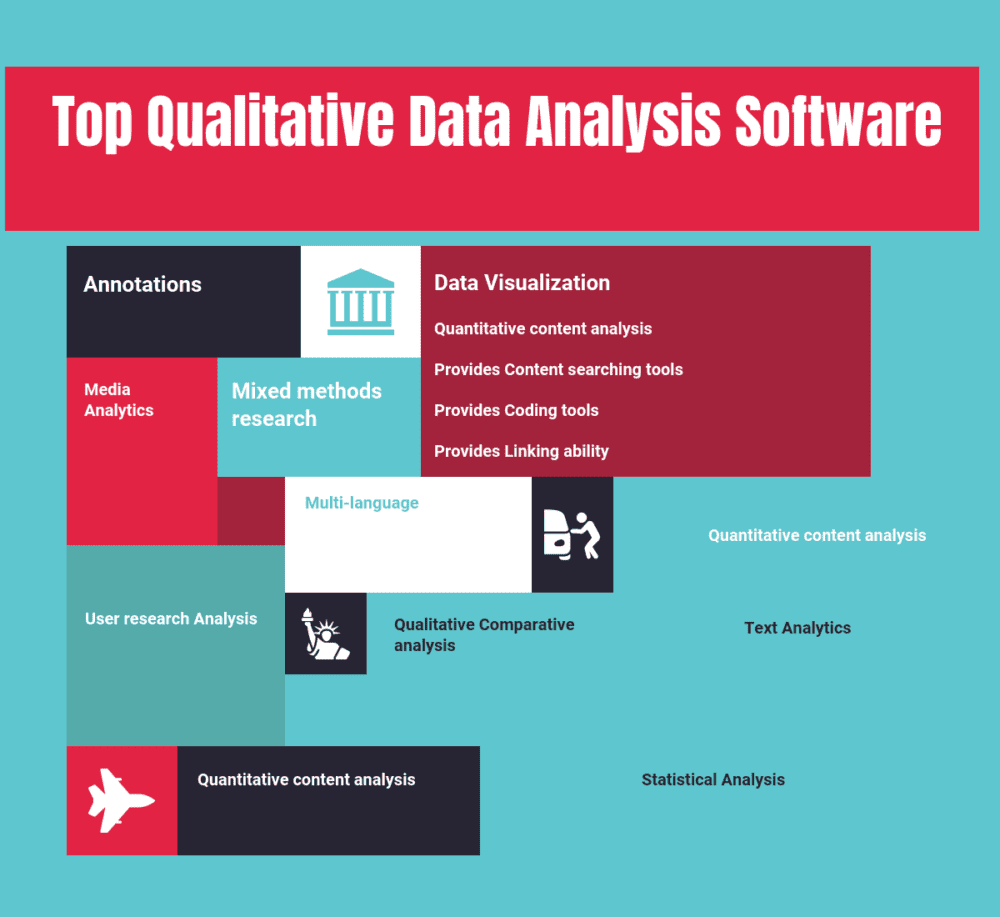
Top 14 Qualitative Data Analysis Software In 2022 Reviews Features Pricing Comparison Pat Research B2b Reviews Buying Guides Best Practices

:max_bytes(150000):strip_icc()/the-5-factors-of-a-good-location.aspx_final2-74156b87934741bbbb6190914c0f823c.png)
Comments
Post a Comment